An electronic handshake has brought together the worlds of automatic identification and capture (AIDC), geomatics, asset mapping, and infrastructure management.
Lauren Bacall once said, “You don’t have to say anything and you don’t have to do anything. Not a thing. Oh, maybe just whistle. You know how to whistle, don’t you?” If only we could just whistle when we need to find and identify a survey monument, or water valve, or underground pipe, or fiber cable … and have that element of infrastructure respond with all of its particulars.This is already happening, and by way of an electromagnetic whistle even dogs can’t hear.
Automatic identification and capture (AIDC) has been with us for decades, from the ubiquitous UPC (Universal Product Code) tags on nearly everything we buy to the electronic tags that foil shoplifters. Entire palettes of products are read as they’re wheeled into the warehouse, lost pets are quickly identified, your baggage is sorted automatically (well, mostly), and even tagged migrating salmon are identified as they pass readers on a fish ladder. People have become so used to idea of intelligent marking systems that a Scandinavian business recently reported that most of its employees have voluntarily opted to have a tiny chip implanted in their hand rather than have to carry a smart card to gain entry to their workplace.
The substantial positive impact of evolving AIDC technologies on commerce is quite obvious, but why would this be a big deal for geomatics, asset mapping, and infrastructure management? Surely one could argue it only takes a moment to identify something in the field and jot down notes in a field book or type in a code on a data collector. But multiply those individual “moments” by several thousand or millions of instances, and we’re talking significant numbers. The geospatial professions have to accept that we live in a mass data capture world where “big data” and the “internet of things” (IoT) have permeated every other aspect of our lives, and the same is being expected of infrastructure and asset management.
To realize the promise of buzz terms like big data and IoT, there must first be data and reliable, durable, and error-free ways to connect the data to physical elements (like utilities, plants, hardware, survey markers, vehicles, and delivery containers) and to the metadata, infrastructure history, and geospatial locations—and preferably in real-time.
The concept of smart data collection is not new. For example, every time a surveyor types in a code like “EC” into his or her data collector in the field and connects that to the location, this enables the downstream drafting software to be able to draw that “edge of concrete” in an automated manner. RFID simply takes this concept further.
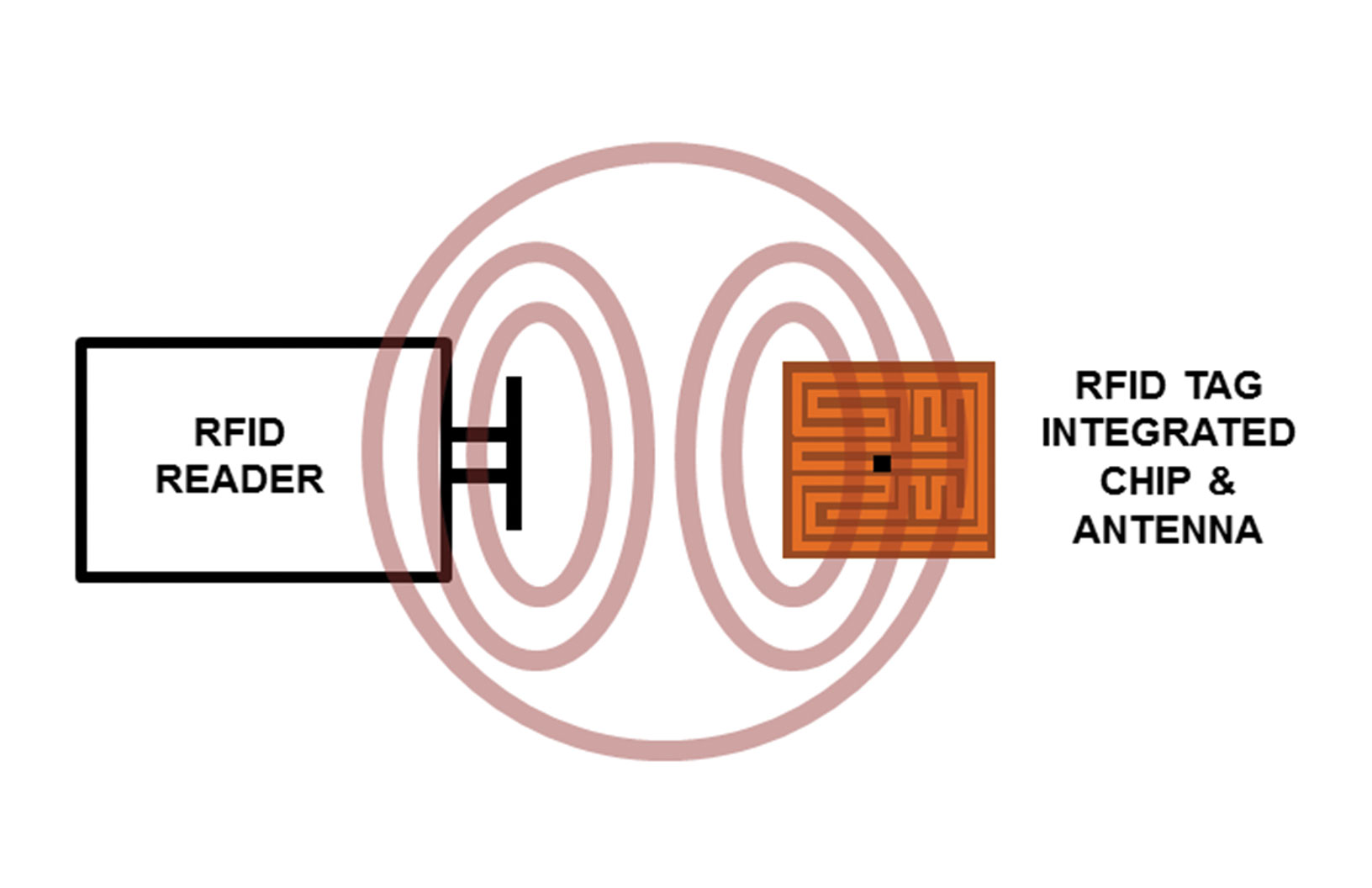
A simplified view of an RFID reader and chip coupling by propagation means, typical of higher frequency systems. Note that the actual chip (shown as a black blip among the antenna pattern of the tag on the right) may be near microscopic.
AIDC Systems
Barcodes, scan codes, and RFID (radio frequency identification) are the most prevalent elements of AIDC systems. The concept is simple: a reader interrogates a tag via a radio signal, light beam, or laser—or simply captures a digital image of the pattern in a tag—and “reads its license plate,” as Mike Klonsinski of Berntsen International puts it.

RFID systems like Berntsen’s
InfraMarker typically come
with enterprise software,
mobile apps, and recommend readers. This TSL 1128 is set up with a cradle for a Samsung smartphone.
“The key to [any of these methods] is that the unique code, number, or ID of the tag can be matched with a database, and this enables a link to a limitless amount of information,” says Klonsinski. “The received data can even trigger further actions.” Klonsinski is the business director of Berntsen International, a company name that may be familiar to many in surveying and infrastructure management for their lines of surveying markers and, more recently, for RFID infrastructure marking and tagging products and software (see “InfraMarker” on page 28).
Barcodes have certain advantages in that they can be very inexpensive, can be printed on demand, and often include a “human readable” code or serial number printed on them for manual verification, if need be. But they are limited to 10 to 30 characters for the typical linear bar-type tags. The main disadvantage is that you need to be able to see/scan the tag clearly.
The more recently deployed scan codes are a 2D version (e.g. QR codes, Maxi-Code, SuperCode) that have the advantage of being able to store up to 7,000 characters in the pattern. But still, there must be line of sight, and these are not well suited for harsh or dirty environments.
Of course, AIDC systems have revolutionized commerce, archiving, cataloguing, warehousing, libraries, and more, but now that electronic tags have become inexpensive to produce, simpler to manage, and durable in even harsh environments, they may soon find their way into nearly every manufactured object, and especially every element of installed infrastructure.
The Aerial Combat Roots of RFID
IFF (Identification Friend or Foe) transponders were deployed on WWII aircraft. Concepts explored in development of these systems led to modern RFID technology.
The concept of radio “interrogation” of a remote object and a validating return signal has its roots in the need to identify combat aircraft as a friend or foe. Several radio signal “pip squeak” methods were tried in the early 20th century. Early patents issued to UK researchers in the 1930s focused on the use of early radar signals to hit uniquely designed reflectors on friendly aircraft, and the returned perturbed signals would verify. But early tests found that there were too many variables in dealing with the reliability of such reflector-based systems due to varied orientation and environmental conditions.
The more practical answer came in the form of radio transponders, receiving and responding with encrypted signals. These systems, deployed by both the Allies and the Axis during WWII, had varied success and later were dubbed “IFF” (Identification Friend or Foe) systems. With combat aircraft flying at such high speeds and particularly in night-time operations, identification by visual methods became impractical. Code wheel arrays were deployed with the transponders of each aircraft, and it is generally believed that such IFF systems gave a slight advantage to the RAF in the Battle of Britain. And when the Allies cracked the IFF code wheels of the Axis, some British night-fighter aircraft fitted with the famed “Perfecto” radios (deployed on De Havilland Mosquito aircraft) could interrogate the enemy IFF transponders.
By the late 1940s, the forerunners of the sophisticated radar-based IFF systems (still in use today) were developed, and proposals for commercial use in aviation, transportation, shipping, and general commerce were soon to follow.
Interrogation and Response
An RFID system includes readers and tags/chips. The reader has an emitter and an antenna, plus an on-board data system to interpret the incoming returned code or a connection to an external data system. Readers can range from fixed systems (e.g. placed around warehouses), high-end handheld devices with internal memory, or even a simple Bluetooth reader (some as small as a key fob) that connect to your phone or mobile device and a database in the cloud.
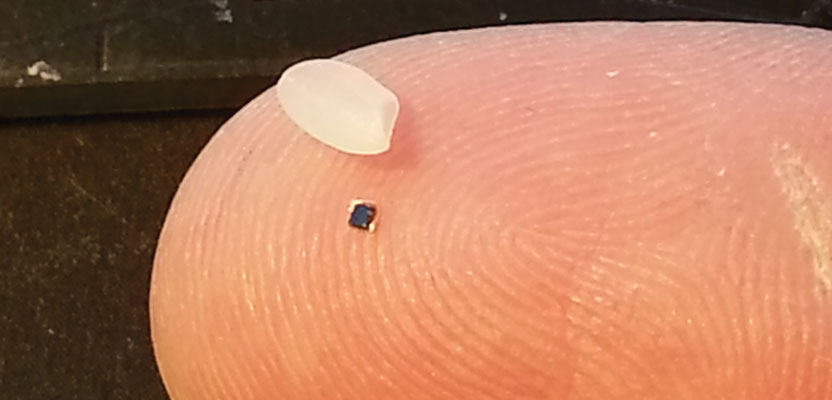
The largest single element of an RFID “chip,” as we can picture them, is the antenna; this might be a small antenna array of a simple metallic pattern on a thin backing. The actual integrated circuit chip may be near-microscopic—it may need to store only a few bytes of information and have few active functions.
In many lower frequency systems, the chip and reader magnetic fields couple in an inductive manner and may contain simple coils to pair in close proximity. In higher frequency systems, like the UHF Gen 2 types popular for infrastructure tagging, the electromagnetic coupling is by propagation means and would include true antennae.
The integrated chip and antenna can be tiny: smaller than a grain of rice, or even smaller than a slice of a grain of rice. It can be “printed,” inlaid foil-thin, or embedded into any manner of casings. For infrastructure like pipelines, valves, pumps, etc, the casings can be made durable for all kinds of harsh conditions and temperature extremes and can be bolted, screwed, epoxied, and moulded into the receiving hardware or attached with a lanyard (like to a valve handle).
RFID can be “active” and include a battery to increase the range of the returned signal and in some cases to act as a beacon. Most that are used for infrastructure tagging are “passive” with the return signal being powered by the tiny amount of electromagnetic energy the chip absorbs from the emissions of the interrogating RFID reader. Some chips are programmable by the end user, but most used for asset tagging are delivered from manufacturers pre-loaded with only a simple unique code, something that works like a serial number or the plate number in the license analogy.
In Berntsen’s implementation they add, “Write more data” beyond the EPC number that comes with the tag. This additional data could include such things as install date, utility type, or other identifying metadata; this helps people who have readers and the appropriate mobile software verify the tag even without access to the cloud.
The unique code alone can still have a lot of utility even though it might seem like a totally meaningless or essentially random number. It gains its function by matching that number to the end-user’s database, like adding a foreign key to an existing geodatabase. For example, a utility adding a valve would have the field crew use a handheld reader with a database of the outside plant loaded on-board or connected via the cloud. As the tag is read (that might have even been added by the valve manufacturer at the factory or in the warehouse), a step is taken to bind that code to the respective record in the database.
There are chips that can have extra data programmed or flashed into them from a reader, but, as with other features, there are trade-offs in cost and durability between active and passive, programmable or pre-programmed chips.
Infrastructure and Underground Utility Tagging
There are particular challenges to tagging infrastructure, especially underground utilities, plants in harsh environments, under water, and metal hardware. RFID solutions for tagging underground utilities (in the 6’ deep range) have been around for many years; tags with embedded RFID chips are frequently attached to underground utilities or plastic balls, and sticks with chips are dropped into the trenches to be shallow enough to read.
As lower frequencies were typically chosen for their penetrating properties, low-frequency solutions had been developed, some using different frequencies to differentiate different types of underground utilities. Low-frequency systems were often slower and required larger and heavier hardware than some newer UHF systems.
Currently, UHF-based systems, particularly UHF Gen 2 Class 1, have seen a substantial amount of development and implementation for plant and utilities. Advances in UHF have now made underground reading viable, which means that—for the first time—underground UHF RFID tags can be used in conjunction with the popular above-ground UHF applications.
Chips are now produced with specialized backings that can work well on, say, a metal pump, pipe, or valve. Some that are purpose-built may not actually work well if not attached to a metal object. Passive chips can be designed to be durable, even in harsh environments, to last many decades.
“RFID chips will probably outlive any of the infrastructures they are attached to,” says Berntsen’s head of research and development, Bill Rushing. “Underground deployment might even extend the life of a chip; there is a fairly consistent temperature and moisture content down there.”
InfraMarker

The application of RFID tags to survey markers can include tags on witness posts and tags embedded in the actual monuments. Here a hand-held UHF reader (with cradled smartphone) can both read and write to RFID tags in the field.
An example of an infrastructure-intelligent marking system is Berntsen’s InfraMarker solution. This UHF Gen 2-based system has passive RFID chips embedded into hardened casings, two types of standalone data collector/readers, and a smart phone or mobile device with software that pairs with the reader and powers the mobile system.
In this example, the InfraMarker mobile app turns on the Bluetooth and pairs it with the selected RFID reader. The mobile app then manages all of the user interface (including the writing, reading of tags, importing the smartphone’s GPS coordinates), attaches photos, video, and other information to the asset record, and sends the record to the cloud.
The key, though, is the middleware: that bridge between the unique ID and the end user’s infrastructure database. While InfraMarker comes with a ready-made mobile app, the middleware is also designed to have enough flexibility to operate as an infrastructure management system or be integrated into a customer’s existing infrastructure asset management and enterprise workflow/work order tracking systems with standard import and export formats.
As geospatial professions have had to learn to adapt to increasingly digital environments, the move to intelligent marking systems was a natural progression for Berntsen International. “This is what we do and have been doing for 40 years,” says Bill Rushing. “We specialize in marking systems, and now with smart-marking products.”
Klonsinski notes that Berntsen has been working with RFID technology since 2006 and has recently patented underground RFID technology to speed the locating of underground assets, and he says, “Now users can ‘smart mark’ above-ground survey monuments and assets tags and below-ground asset marking tags using the same UHF system.”